介绍了业务接口工作在三层,上行连接路由器(OSPF),下行连接交换机的主备备份组网的CLI举例。
组网需求
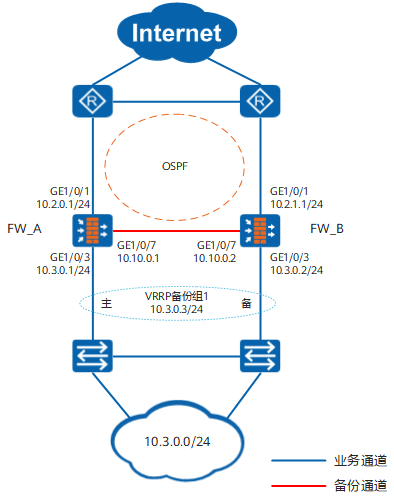
如图1所示,两台FW的业务接口都工作在三层,上行连接路由器,下行连接二层交换机。FW与路由器之间运行OSPF协议。现在希望两台FW以主备备份方式工作。正常情况下,流量通过FW_A转发。当FW_A出现故障时,流量通过FW_B转发,保证业务不中断。
操作步骤
- 完成网络基本配置。
FW_A
FW_B
# 配置FW各接口的IP地址。
<FW_A> system-view [FW_A] interface GigabitEthernet 1/0/1 [FW_A-GigabitEthernet1/0/1] ip address 10.2.0.1 24 [FW_A-GigabitEthernet1/0/1] quit [FW_A] interface GigabitEthernet 1/0/3 [FW_A-GigabitEthernet1/0/3] ip address 10.3.0.1 24 [FW_A-GigabitEthernet1/0/3] quit [FW_A] interface GigabitEthernet 1/0/7 [FW_A-GigabitEthernet1/0/7] ip address 10.10.0.1 24 [FW_A-GigabitEthernet1/0/7] quit
<FW_B> system-view [FW_B] interface GigabitEthernet 1/0/1 [FW_B-GigabitEthernet1/0/1] ip address 10.2.1.1 24 [FW_B-GigabitEthernet1/0/1] quit [FW_B] interface GigabitEthernet 1/0/3 [FW_B-GigabitEthernet1/0/3] ip address 10.3.0.2 24 [FW_B-GigabitEthernet1/0/3] quit [FW_B] interface GigabitEthernet 1/0/7 [FW_B-GigabitEthernet1/0/7] ip address 10.10.0.2 24 [FW_B-GigabitEthernet1/0/7] quit
# 将FW各接口加入相应的安全区域。
[FW_A] firewall zone trust [FW_A-zone-trust] add interface GigabitEthernet 1/0/3 [FW_A-zone-trust] quit [FW_A] firewall zone dmz [FW_A-zone-dmz] add interface GigabitEthernet 1/0/7 [FW_A-zone-dmz] quit [FW_A] firewall zone untrust [FW_A-zone-untrust] add interface GigabitEthernet 1/0/1 [FW_A-zone-untrust] quit
[FW_B] firewall zone trust [FW_B-zone-trust] add interface GigabitEthernet 1/0/3 [FW_B-zone-trust] quit [FW_B] firewall zone dmz [FW_B-zone-dmz] add interface GigabitEthernet 1/0/7 [FW_B-zone-dmz] quit [FW_B] firewall zone untrust [FW_B-zone-untrust] add interface GigabitEthernet 1/0/1 [FW_B-zone-untrust] quit
# 在FW上配置OSPF,保证路由可达。
[FW_A] ospf 10 [FW_A-ospf-10] area 0 [FW_A-ospf-10-area-0.0.0.0] network 10.2.0.0 0.0.0.255 [FW_A-ospf-10-area-0.0.0.0] network 10.3.0.0 0.0.0.255 [FW_A-ospf-10-area-0.0.0.0] quit [FW_A-ospf-10] quit
[FW_B] ospf 10 [FW_B-ospf-10] area 0 [FW_B-ospf-10-area-0.0.0.0] network 10.2.1.0 0.0.0.255 [FW_B-ospf-10-area-0.0.0.0] network 10.3.0.0 0.0.0.255 [FW_B-ospf-10-area-0.0.0.0] quit [FW_B-ospf-10] quit
- 配置双机热备功能。
由于FW上行连接路由器,下行连接交换机,因此需要在FW上配置VGMP组监控上行接口,并在下行接口上配置VRRP备份组。
FW_A
FW_B
# 在FW上配置VGMP组监控上行业务接口。
[FW_A] hrp track interface GigabitEthernet 1/0/1[FW_B] hrp track interface GigabitEthernet 1/0/1# 在FW_A下行业务接口GE1/0/3上配置VRRP备份组1,并将其状态设置为Active。在FW_B下行业务接口GE1/0/3上配置VRRP备份组1,并将其状态设置为Standby。
[FW_A] interface GigabitEthernet 1/0/3 [FW_A-GigabitEthernet1/0/3] vrrp vrid 1 virtual-ip 10.3.0.3 active [FW_A-GigabitEthernet1/0/3] quit
[FW_B] interface GigabitEthernet 1/0/3 [FW_B-GigabitEthernet1/0/3] vrrp vrid 1 virtual-ip 10.3.0.3 standby [FW_B-GigabitEthernet1/0/3] quit
# 在FW上配置根据VGMP状态调整OSPF Cost值功能。
[FW_A] hrp adjust ospf-cost enable[FW_B] hrp adjust ospf-cost enable# 在FW上指定心跳口并启用双机热备功能。
[FW_A] hrp interface GigabitEthernet 1/0/7 remote 10.10.0.2 [FW_A] hrp enable
[FW_B] hrp interface GigabitEthernet 1/0/7 remote 10.10.0.1 [FW_B] hrp enable
- 在FW_A上配置安全策略。双机热备状态成功建立后,FW_A的安全策略配置会自动备份到FW_B上。
# 配置安全策略,允许内网用户访问外网。
HRP_M[FW_A] security-policy HRP_M[FW_A-policy-security] rule name policy_sec1 HRP_M[FW_A-policy-security-rule-policy_sec1] source-zone trust HRP_M[FW_A-policy-security-rule-policy_sec1] destination-zone untrust HRP_M[FW_A-policy-security-rule-policy_sec1] source-address 10.3.0.0 24 HRP_M[FW_A-policy-security-rule-policy_sec1] action permit HRP_M[FW_A-policy-security-rule-policy_sec1] quit
# 配置安全策略,允许FW与上行路由器(部署在untrust区域)交互OSPF报文。
OSPF报文是否受安全策略控制决定于firewall packet-filter basic-protocol enable命令的配置。缺省情况下,firewall packet-filter basic-protocol enable处于开启状态,即OSPF报文受安全策略控制,需要在上行业务接口所在安全区域untrust与local区域之间配置安全策略,允许协议类型为OSPF报文通过。本例以firewall packet-filter basic-protocol enable开启为例进行介绍。
HRP_M[FW_A-policy-security] rule name policy_sec2 HRP_M[FW_A-policy-security-rule-policy_sec2] source-zone local untrust HRP_M[FW_A-policy-security-rule-policy_sec2] destination-zone local untrust HRP_M[FW_A-policy-security-rule-policy_sec2] service ospf HRP_M[FW_A-policy-security-rule-policy_sec2] action permit
- 配置路由器和交换机。
# 在路由器上配置OSPF,发布相邻网段,具体配置命令请参考路由器的相关文档。
# 在交换机上将三个接口加入同一个VLAN,具体配置命令请参考交换机的相关文档。
结果验证
-
在FW_A和FW_B上执行display vrrp命令,检查VRRP组内接口的状态信息,显示以下信息表示VRRP组建立成功。
FW_A
FW_B
HRP_M<FW_A> display vrrp GigabitEthernet1/0/3 | Virtual Router 1 State : Master Virtual IP : 10.3.0.3 Master IP : 10.3.0.1 PriorityRun : 120 PriorityConfig : 100 MasterPriority : 120 Preempt : YES Delay Time : 0 s TimerRun : 60 s TimerConfig : 60 s Auth type : NONE Virtual MAC : 0000-5e00-0101 Check TTL : YES Config type : vgmp-vrrp Backup-forward : disabled Create time : 2018-03-17 17:35:54 UTC+08:00 Last change time : 2018-03-22 16:01:56 UTC+08:00HRP_S<FW_B> display vrrp GigabitEthernet1/0/3 | Virtual Router 1 State : Backup Virtual IP : 10.3.0.3 Master IP : 10.3.0.1 PriorityRun : 120 PriorityConfig : 100 MasterPriority : 120 Preempt : YES Delay Time : 0 s TimerRun : 60 s TimerConfig : 60 s Auth type : NONE Virtual MAC : 0000-5e00-0101 Check TTL : YES Config type : vgmp-vrrp Backup-forward : disabled Create time : 2018-03-17 17:37:54 UTC+08:00 Last change time : 2018-03-22 16:03:56 UTC+08:00 -
在FW_A和FW_B上执行display hrp state verbose命令,检查当前VGMP组的状态,显示以下信息表示双机热备建立成功。
FW_A
FW_B
HRP_M<FW_A> display hrp state verbose Role: active, peer: standby Running priority: 45000, peer: 45000 Backup channel usage: 30% Stable time: 1 days, 13 hours, 35 minutes Last state change information: 2018-03-22 16:01:56 HRP core state changed, old_ state = normal(standby), new_state = normal(active), local_priority = 45000, peer_priority = 45000. Configuration: hello interval: 1000ms preempt: 60s mirror configuration: off mirror session: off track trunk member: on auto-sync configuration: on auto-sync connection-status: on adjust ospf-cost: on adjust ospfv3-cost: on adjust bgp-cost: on nat resource: off Detail information: GigabitEthernet1/0/3 vrrp vrid 1: active GigabitEthernet1/0/1: up ospf-cost: +0HRP_S<FW_B> display hrp state verbose Role: standby, peer: active Running priority: 45000, peer: 45000 Backup channel usage: 30% Stable time: 1 days, 13 hours, 35 minutes Last state change information: 2018-03-22 16:01:56 HRP core state changed, old_ state = normal(standby), new_state = normal(standby), local_priority = 45000, peer_priority = 45000. Configuration: hello interval: 1000ms preempt: 60s mirror configuration: off mirror session: off track trunk member: on auto-sync configuration: on auto-sync connection-status: on adjust ospf-cost: on adjust ospfv3-cost: on adjust bgp-cost: on nat resource: off Detail information: GigabitEthernet1/0/3 vrrp vrid 1: standby GigabitEthernet1/0/1: up ospf-cost: +65500
配置脚本
|
FW_A |
FW_B |
|---|---|
# hrp enable hrp interface GigabitEthernet 1/0/7 remote 10.10.0.2 hrp track interface GigabitEthernet 1/0/1 # interface GigabitEthernet 1/0/1 ip address 10.2.0.1 255.255.255.0 # interface GigabitEthernet 1/0/3 ip address 10.3.0.1 255.255.255.0 vrrp vrid 1 virtual-ip 10.3.0.3 active # interface GigabitEthernet 1/0/7 ip address 10.10.0.1 255.255.255.0 # firewall zone trust set priority 85 add interface GigabitEthernet 1/0/3 # firewall zone untrust set priority 5 add interface GigabitEthernet 1/0/1 # firewall zone dmz set priority 50 add interface GigabitEthernet1/0/7 # ospf 10 area 0.0.0.0 network 10.2.0.0 0.0.0.255 network 10.3.0.0 0.0.0.255 # security-policy rule name policy_sec1 source-zone trust destination-zone untrust source-address 10.3.0.0 24 action permit rule name policy_sec2 source-zone local source-zone untrust destination-zone local destination-zone untrust service ospf action permit |
# hrp enable hrp interface GigabitEthernet 1/0/7 remote 10.10.0.1 hrp track interface GigabitEthernet 1/0/1 # interface GigabitEthernet 1/0/1 ip address 10.2.1.1 255.255.255.0 # interface GigabitEthernet 1/0/3 ip address 10.3.0.2 255.255.255.0 vrrp vrid 1 virtual-ip 10.3.0.3 standby # interface GigabitEthernet 1/0/7 ip address 10.10.0.2 255.255.255.0 # firewall zone trust set priority 85 add interface GigabitEthernet 1/0/3 # firewall zone untrust set priority 5 add interface GigabitEthernet 1/0/1 # firewall zone dmz set priority 50 add interface GigabitEthernet1/0/7 # ospf 10 area 0.0.0.0 network 10.2.1.0 0.0.0.255 network 10.3.0.0 0.0.0.255 # security-policy rule name policy_sec1 source-zone trust destination-zone untrust source-address 10.3.0.0 24 action permit rule name policy_sec2 source-zone local source-zone untrust destination-zone local destination-zone untrust service ospf action permi |